Critical RCE Bug Affects Millions of OpenWrt-based Network Devices
A cybersecurity researcher today disclosed technical details and proof-of-concept of a critical remote code execution vulnerability affecting OpenWrt, a widely used Linux-based operating system for routers, residential gateways, and other embedded devices that route network traffic.
Tracked as CVE-2020-7982, the vulnerability resides in the OPKG package manager of OpenWrt that exists in the way it performs integrity checking of downloaded packages using the SHA-256 checksums embedded in the signed repository index.
While an 'opkg install' command is invoked on the victim system, the flaw could allow a remote man-in-the-middle attacker in a position to intercept the communication of a targeted device to execute arbitrary code by tricking the system into installing a malicious package or software update without verification.
If exploited successfully, a remote attacker could gain complete control over the targeted OpenWrt network device, and subsequently, over the network traffic it manages.
The three-year-old vulnerability was discovered earlier this year by Guido Vranken from the ForAllSecure software company, who then reported it responsibly to the OpenWrt development team.
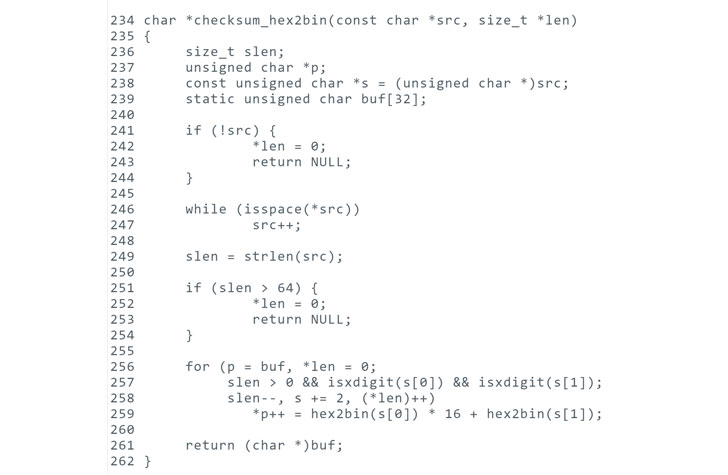
In a blog post published today, Vranken explained that when a checksum contains any leading spaces, OPKG on the vulnerable versions of OpenWrt skips checking the integrity of the downloaded package and proceeds to the installation task.
"Due to the fact that opkg on OpenWrt runs as root and has write access to the entire filesystem, arbitrary code could be injected by means of forged .ipk packages with a malicious payload," OpenWrt team said.
The remote exploitation of this vulnerability is possible due to the fact that integrity in Linux based software installation mechanisms rely on digitally signing files while downloading files over the insecure HTTP connection.
Besides this, to exploit the vulnerability, attackers also need to serve a malicious package with the size equals to that specified in the package list on downloads.openwrt.org.
According to the project team, OpenWrt versions 18.06.0 to 18.06.6 and 19.07.0, as well as LEDE 17.01.0 to 17.01.7, are affected.
To fix this issue, affected users are advised to upgrade their device firmware to the latest OpenWrt versions 18.06.7 and 19.07.1, which were released last month.
Tracked as CVE-2020-7982, the vulnerability resides in the OPKG package manager of OpenWrt that exists in the way it performs integrity checking of downloaded packages using the SHA-256 checksums embedded in the signed repository index.
While an 'opkg install' command is invoked on the victim system, the flaw could allow a remote man-in-the-middle attacker in a position to intercept the communication of a targeted device to execute arbitrary code by tricking the system into installing a malicious package or software update without verification.
If exploited successfully, a remote attacker could gain complete control over the targeted OpenWrt network device, and subsequently, over the network traffic it manages.
The three-year-old vulnerability was discovered earlier this year by Guido Vranken from the ForAllSecure software company, who then reported it responsibly to the OpenWrt development team.
In a blog post published today, Vranken explained that when a checksum contains any leading spaces, OPKG on the vulnerable versions of OpenWrt skips checking the integrity of the downloaded package and proceeds to the installation task.
"Due to the fact that opkg on OpenWrt runs as root and has write access to the entire filesystem, arbitrary code could be injected by means of forged .ipk packages with a malicious payload," OpenWrt team said.
The remote exploitation of this vulnerability is possible due to the fact that integrity in Linux based software installation mechanisms rely on digitally signing files while downloading files over the insecure HTTP connection.
Besides this, to exploit the vulnerability, attackers also need to serve a malicious package with the size equals to that specified in the package list on downloads.openwrt.org.
According to the project team, OpenWrt versions 18.06.0 to 18.06.6 and 19.07.0, as well as LEDE 17.01.0 to 17.01.7, are affected.
"As a stopgap solution, OpenWRT removed the space in the SHA256sum from the package list shortly after I reported the bug," Vranken said.
"However, this is not an adequate long-term solution because an attacker can simply provide an older package list that was signed by the OpenWRT maintainers."
To fix this issue, affected users are advised to upgrade their device firmware to the latest OpenWrt versions 18.06.7 and 19.07.1, which were released last month.
Have something to say about this article? Comment below or share it with us on Facebook, Twitter or our LinkedIn Group.